What is Business Identity Fraud?
Identity fraud is a crime where one person uses another person’s personal data, without authorization, to deceive or defraud someone else. For example, it is identity fraud to use someone’s personal information to open a credit card account without permission, and then charge merchandise to that account.
Identity fraud is also being used on corporate scale, where someone pretends to be an employee of a certain company. This can be a CEO/CFO/… but just as well any other type of employee. By using a fake identity the attacker will try to receive goods or money from his victim. This is Business Identity Fraud. Your business could suffer major financial losses if it fell victim to a Business Identity Fraud attack. Most often, Business Identity Fraud scams are not discovered until it’s too late. As a result, lost funds resulting from the scams are nearly impossible to recover.
2 Techniques to Impersonate Someone
Social Engineering
Fraudsters perform online research to gather as much information as possible about a company and its employees (e.g. on LinkedIn, Google, Facebook, the company website; etc.). With the information they gathered they are able to create a fake identity which is similar to a legitimate one. A second step would be to register a similar domain with similar e-mail addresses. In case the stakes are high, they could even create a new corporate website and fake LinkedIn profiles, to make the fake identity more convincing.
Business E-mail Compromise
Fraudsters use hacking techniques to gain access to a legitimate business e-mail account. This might include malware, phishing campaigns or abusing software vulnerabilities. From this hacked account they gather internal company intelligence and use it to send e-mails to other parties for a fraudulous scheme.
3 Types of Targets for Impersonation
Generally the fraudsters will steal the identity of certain types of employees
High Ranked Employee
CEO Fraud
The most common Business Identity Fraud scams are the ones that impersonate a company’s CEO, CFO or financial adviser to request fake wire transfers. Fake e-mails are sent to the Finance Department requesting immediate payments and complete confidentiality.
Company Purchaser
Fake Order Scam: 3 victims
Fake order scams are the ones that impersonate a company’s purchaser to request fake orders at a supplier company. The goods that are delivered to this ‘large client’ will never be paid.The (well-known) impersonated company is, after investigation, not aware of the fake order and will refuse to pay. The transport company who delivered or stored the goods will never be paid either.
Supplier
Suppliers Fraud / Invoice Fraud
This variant targets businesses working with (foreign) suppliers and/or businesses that regularly perform wire transfer payments. The fraudster tries to convince the Purchase, Accounting or Credit Department to wire the amount due (open invoices) to a new bank account number (sometimes a factoring company).
4 Ways i-Force can help
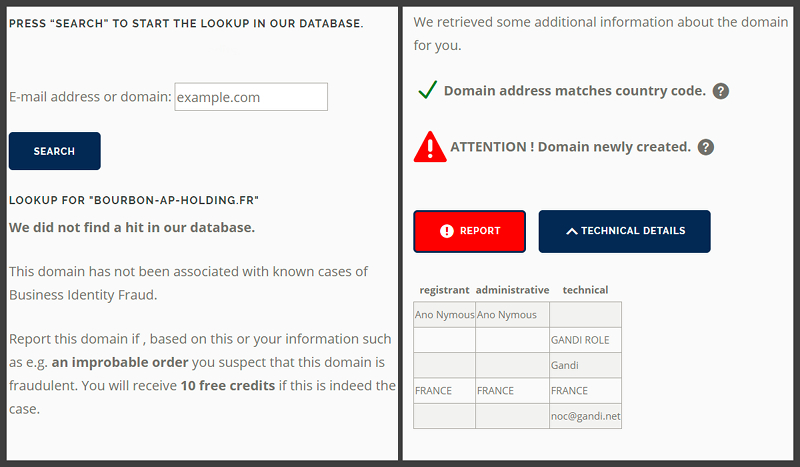
Central Hub to verify and report proven fake domain names
The ID Fraud Check has been put in place to provide businesses with a reliable and easy-to-use reporting and consulting mechanism. The quality of the data is directly attributable to the information ingested via this platform. I-Force staff analyzes the data, striving to identify trends (common used domain names or delivery addresses) and secondly acts as an early warning system to its subscribers.
Based on its experience, i-Force will assist you in managing the case.
Your identity is abused
- ► Report to the board and senior management on the incident, steps taken, and further actions to be carried out.
- ► Communicate towards your stakeholders (vendors, clients,…)
- ► Block all proven false domain names
You are a victim
- ► Warn the next link in the transport chain ASAP & attempt to locate the goods and freeze the delivery to the next level.
- ► Warn your suppliers and use our standard letters
- ► Mitigate further loss by contacting the bank to freeze accounts
- ► Document and complete information related to the fraud case to file a complaint and to support law enforcement.
- ► Digital Forensics to check for infected devices and take necessary security measures.
- ► Check for possible internal collusion.
- ► Report to the board and senior management on the incident, steps taken, and further actions to be carried out
We have developed awareness training for employees located in tactical positions (Finance, Procurement, Sales etc.), focusing on:
- ► Red Flags
- ► Basics of cyber -and email security
- ► Specific internal controls
We can also trigger your employees with a continuous simulated phishing exercise.
i-Force Digital Security Scan
If a company e-mail account was compromised (“hacked”), i-Force can advise you on immediate action steps and help prevent compromises in the future.
5 Assets i-Force brings to the table
i-Force provides partners an early warning system which will notify you when a similar domain as your company domain is actively contacting suppliers.
I-Force can help you
Assets that are defrauded by a fake order scam are almost never sent directly to the fraudster, but rather shipped through multiple locations, joining other similarly defrauded shipments, and eventually culminating at a location where they are picked up by the fraudster.
With asset tracing and recovery we aim to alert the upper links in the transport chain in a timely fashion, so the shipments can be halted before they are passed on. It can however only be successful if acted quickly. The more links we can alert in the chain, the more shipments we can identify as being the result of a fake order scam. This also includes shipments where the supplier is not even aware yet that he was the victim of a scam.
As an independent Belgian based fraud audit firm with over 15 years of experience in the fight against corporate fraud, we dealt with more than 1.300 cases for corporate and governmental clients.
We have a multidisciplinary team of fraud investigators, forensic technology specialists, criminologists and coordinate a pool of licensed private detectives.
By reporting fraud (attempt) cases to i-Force we enlarge our network of intervening companies and create a bigger possibility to warn in an early stage more potential victims.
Become part of our network.
Together we can beat this type of fraud !
In order to ensure maximum effectiveness and efficiency we rely on our extensive network of private detectives, European forensic service firms and specialized security equipment providers.